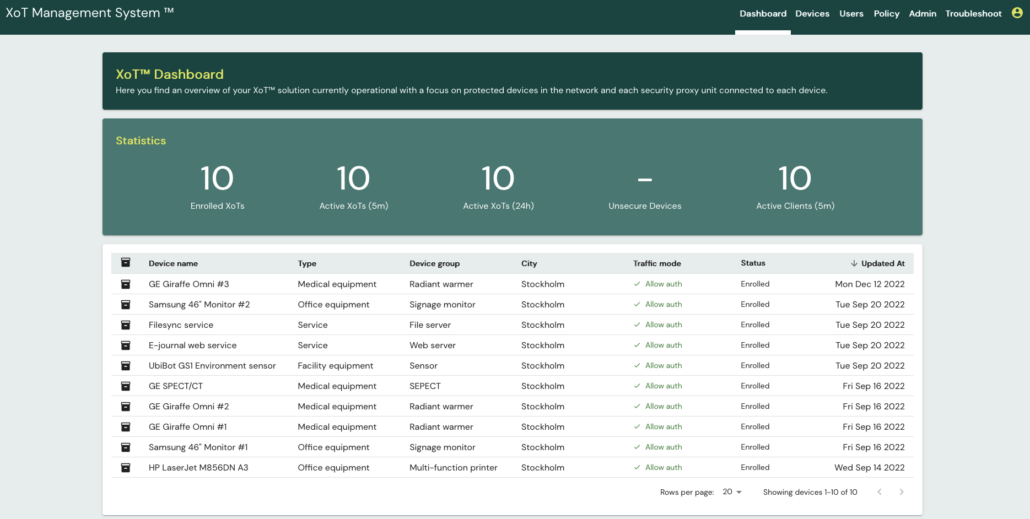
Management System
At the heart of the XoT solution is the XMS (XoT Management System), a policy based management platform that allows or denies access to secured devices.
The XMS handles and supports five distinct tasks;
- Enrolment of new devices
- Life cycle management of existing devices and certificates
- Creating and maintaining access rights through policies
- Asset management of protected equipment
- Collecting security data from XoT devices
The XMS can be operated on any modern platform using Kubernetes or VMs, on-prem or in the cloud, based on customer requirements.